As an analyst, I’ve noticed a pattern whenever a large crypto platform gets hacked. It almost always follows the same script. Within a day or two, you see a serious post on X claiming they were hit by a very advanced, potentially state-backed cyberattack. What they’re really saying, though, is that it was likely the Lazarus Group.
As an analyst, I’ve noticed a troubling pattern in the crypto space: whenever a security breach happens, North Korea often becomes the default scapegoat. It’s a convenient excuse. Let’s be honest, admitting a simple mistake – like an employee accidentally exposing private keys – is devastating for reputations. But claiming a sophisticated attack by a nation-state, even without solid proof, tends to garner sympathy, buys time to fix the problem, and shields companies from investor backlash. It’s become a surprisingly common way to avoid accountability.
Is Lazarus Group truly responsible for the majority of the billion-dollar cyberattacks plaguing the industry, or is the name simply being used as an easy excuse for the industry’s own security failures?
Based on evidence from FBI and DOJ cases, reports from Chainalysis, Elliptic, and TRM Labs, and investigations into attacks on LayerZero and Drift, it’s clear that the Lazarus Group is a real entity. They are linked to North Korea and have been responsible for many of the biggest cryptocurrency thefts on record, though not every single one.
Who actually is the Lazarus Group?

As a crypto investor, I’ve been keeping a close eye on the group known as Lazarus – they’re also called APT38, TraderTraitor, and UNC4736. It’s important to understand they aren’t just some random hackers. They’re a really well-organized operation, backed by the North Korean government, specifically through their Reconnaissance General Bureau and a unit called Bureau 121. It’s a serious, state-sponsored threat, not a bunch of individuals acting alone.
This group first became well-known for the 2014 Sony Pictures hack and the 2017 WannaCry ransomware attack. By around 2018, they began focusing on cryptocurrency. The reason was clear: North Korea is subject to strict international sanctions, and cryptocurrency provides a way to move large sums of money across borders without the restrictions of traditional banking – a critical need for funding its nuclear weapons and missile programs.
Evidence from U.S. legal cases, analysis of malicious software, tracking internet addresses, and intelligence gathering all connect the Lazarus hacking group to North Korea. While North Korea claims it isn’t involved, data from blockchain technology consistently suggests otherwise.
The Scoreboard: $7.3 billion and counting
The group’s financial footprint is substantial.
North Korean hackers stole a staggering $2.02 billion in cryptocurrency in 2025, a 51% increase from the previous year. This activity accounted for about 76% of all crypto thefts related to online services during that time, bringing their total earnings from these hacks to $6.75 billion by the end of last year, according to data from Chainalysis.
In April 2026, two major cyberattacks – one on Kelp DAO and another on Drift Protocol – resulted in around $575 million in losses within just 17 days. This brought the total amount stolen by the group, known as Lazarus, to over $7.3 billion, making it one of the most successful cyber-theft operations ever recorded.
A clear trend has emerged: fewer attacks, but significantly higher value per incident.
The big heists: A verified table
This report details significant cryptocurrency thefts linked to the Lazarus Group, based on information from the FBI, Department of Justice, and forensic analyses by Chainalysis, Elliptic, and TRM Labs. It also incorporates insights from victim reports and direct blockchain data.
| Rank | Target | Date | Amount | Method |
| 1 | Bybit Exchange | Feb 2025 | $1.5B | Safe{Wallet} supply chain compromise and social engineering |
| 2 | Ronin Bridge (Axie Infinity) | Mar 2022 | $620 to $625M | Validator key theft via fake-job spear phishing |
| 3 | DMM Bitcoin | May 2024 | ~$308M | Hot wallet compromise |
| 4 | Kelp DAO (rsETH) | Apr 18, 2026 | $290 to $292M | RPC node poisoning and DDoS on LayerZero DVNs |
| 5 | Drift Protocol | Apr 1, 2026 | $285M | Six-month social engineering of Security Council multisig |
| 6 | KuCoin Exchange | Sep 2020 | ~$275M | Hot wallet breach |
| 7 | WazirX | Jul 2024 | ~$235M | Wallet compromise |
| 8 | Harmony Horizon Bridge | Jun 2022 | $100M | Private key theft |
| 9 | Atomic Wallet | Jun 2023 | ~$100M | Malware and supply chain attack |
| 10 | Alphapo | Jul 2023 | $60M | Payment platform breach |
While larger attacks dominate the headlines, smaller breaches like those affecting Stake.com ($41 million in 2023) and Upbit ($36-$37 million in 2025) follow similar trends. The Poly Network hack, which involved $600 million in August 2021, is often linked to the Lazarus Group in news reports, but proving their involvement is less certain than in the other cases.
A consistent pattern links nearly all the confirmed hacks on this list, but it hasn’t been widely reported in crypto media: a 45-day money laundering process. This involves moving funds between wallets, using mixers to obscure the source, and then cashing out in small amounts through over-the-counter networks in Asia. It’s a telltale sign, repeatedly appearing in connection with these thefts.
Why “Lazarus = every hack” feels overblown
While Lazarus Group isn’t behind every cryptocurrency hack, many smaller attacks are done by individual hackers. Figuring out who’s responsible is difficult, and it’s even possible for attackers to deliberately mislead investigators. But when experts confidently identify a group, it’s usually based on strong evidence from several sources, like tracking transactions on the blockchain, analyzing the code used in attacks, and information from intelligence agencies.
Evidence from the April 2026 attacks on Drift Protocol and Kelp DAO, combined with investigations and information released by the projects themselves, points to the work of the Lazarus Group, a known hacking organization.
How investigators attribute attacks to Lazarus
How do forensic experts actually confirm a cyberattack is the work of the Lazarus Group, and not just blamed on them? They focus on specific patterns of behavior – the tactics, techniques, and procedures used in the attack. It’s about finding concrete digital evidence, not just making assumptions.
Lazarus often uses the same malware in multiple attacks. A prime example is AppleJeus, a previously identified fake cryptocurrency app. This practice of reusing code provides valuable clues about their activities.
This group doesn’t simply move stolen money; they follow consistent, recognizable patterns. They previously used Tornado Cash to move hundreds of millions of dollars, but after it was sanctioned, they quickly switched to other privacy tools like Railgun and increased their use of Bitcoin and certain over-the-counter (OTC) brokers in Asia. This shift isn’t random – it demonstrates that the same people are behind the laundering, not just copycats.
A disturbing trend involves hackers directly infiltrating crypto companies by getting hired as employees. Instead of relying on complicated hacking techniques, the Lazarus group has been creating false identities and resumes to land remote IT jobs within DeFi teams and crypto businesses. Once inside, they quietly gain access to systems and steal funds. This tactic became clear through several incidents in 2024 and 2025.
Similarities in underlying infrastructure – like shared IP addresses, web hosting, payment processing, and network connections – are common. Investigations rarely rely on just one piece of evidence; they usually involve looking at multiple different factors.
For years, no solid evidence has successfully disproven claims attributed to Lazarus. It’s worth considering this carefully.
The limits of the scapegoat theory
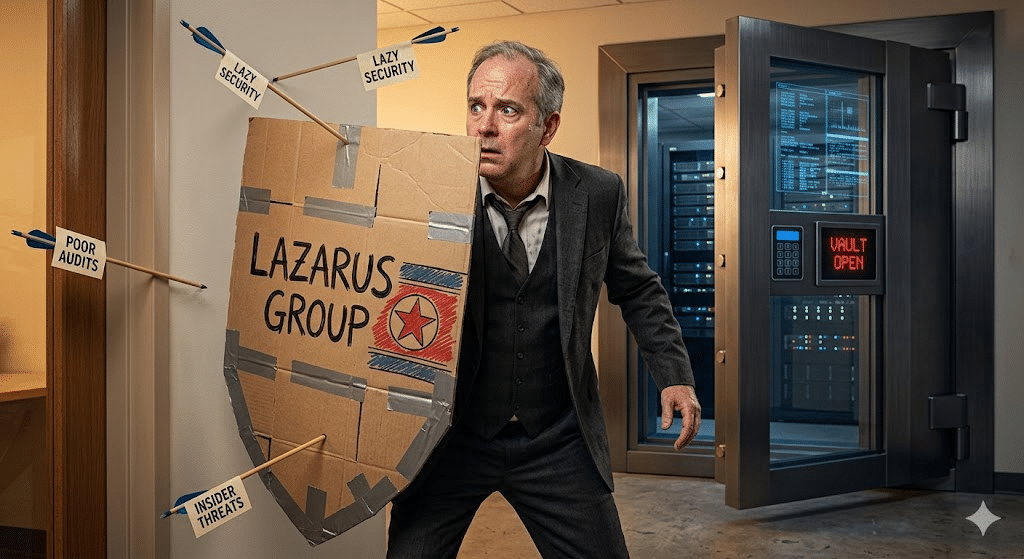
It’s important to understand this carefully. While the Lazarus Group is a genuine threat, they aren’t everywhere. Many companies prefer to blame “nation-state actors” to avoid taking responsibility for their own security failures.
The incentive structures are obvious once you look at them:
When a cyberattack happens, describing it as an act of war by another country can be a better way to calm investors than admitting to a simple phishing scam. This approach downplays the severity of the security failure in a way that’s more palatable to those who have invested money.
When rules are lacking, it’s common to see projects fail with sudden ‘exit scams’ or be sabotaged from within. It’s often easier to point the finger at external actors, like North Korea, to hide these internal issues after things go wrong.
Often, security breaches aren’t due to sophisticated attacks, but simple mistakes like falling for phishing emails or careless handling of multi-signature wallets. It’s difficult to admit to basic errors – like an employee clicking a malicious link – when publicly announcing funding or success.
Let’s look at the numbers. In 2025, around $3.4 billion was stolen in the crypto world, and about $1.38 billion of that came from sources other than North Korea. This included amateur hackers, Russian criminal groups, Chinese money laundering operations, people with inside knowledge, and common thieves. Therefore, it doesn’t make sense for projects to automatically blame the Lazarus Group for every security issue, as the data doesn’t support that claim.
Finding the right balance is key. Lazarus is known for pulling off very large hacks – those worth millions or even billions. However, they aren’t involved in the smaller scams, like exploiting simple vulnerabilities, internal team thefts, or bugs in the code – which actually make up most of the problems in the DeFi space. Those types of incidents are usually carried out by individuals, those looking for quick opportunities, or sometimes even the project teams themselves.
April 2026: Two textbook Lazarus attacks
The two April mega-hits are almost perfect case studies of how Lazarus operates in 2026.
On April 1st, Drift Protocol lost $285 million due to a sophisticated attack that didn’t involve any flaws in its code. Instead, attackers spent six months using social engineering – manipulating people – to gain access through members of the protocol’s Security Council. Within days, three blockchain analysis firms – Elliptic, TRM Labs, and Chainalysis – all found evidence linking the attack to a group associated with North Korea.
On April 18th, Kelp DAO suffered a loss of between $290 and $292 million due to an attack that targeted LayerZero’s network. The attackers used a combination of techniques – compromising network nodes and overwhelming the system with traffic – to send fake messages between blockchains and steal rsETH. LayerZero believes the attack was carried out by TraderTraitor, a group linked to the Lazarus hacking organization.
As an analyst, I’ve been closely following these recent attacks, and they really demonstrate how much this group has changed. They’ve gone beyond simply finding flaws in code; they’re now engaging in full-blown operational warfare. We’re seeing them target people, mess with critical infrastructure, and run incredibly patient, months-long campaigns. Frankly, this is a completely new type of threat that the DeFi space wasn’t originally designed to handle.
What it means going forward
North Korea views cryptocurrency as a major source of income, helping it fund activities despite international sanctions. This is significant because it indicates that the hacking group Lazarus, linked to North Korea, isn’t likely to stop its operations – and may even be increasing them, as suggested by recent activity in April 2026.
Security practices need to evolve, especially for online protocols. We need to verify multiple decentralized validator networks, use hardware-protected multi-signature setups, and require regular social engineering training for all administrators. It’s also crucial to simulate attacks as if a sophisticated attacker is already within our systems – something that’s happening more and more frequently. Recently, overlooking red flags – like fake job postings or unusual internal communications – cost the industry over $575 million in just one month.
Look, as a crypto investor, I’m seeing things get serious. I’m now convinced a hardware wallet isn’t a luxury – it’s a must-have. I’m double-checking *every* transaction approval myself, and honestly, I’m way more cautious about job offers in this space, especially if they’re for developers who could get their hands on important keys. You really need to be careful who you trust.
The crypto industry is seeing a small improvement in recovering stolen funds. While quicker data analysis, faster responses to sanctions, better bug bounty programs, and increased public scrutiny from blockchain investigators are sometimes helping to reclaim lost assets, it’s often not fast enough. Most projects still react to attacks from groups like Lazarus as if they were typical DeFi hacks, and this delay is costing the industry billions.
Bottom line
The Lazarus Group is a real and highly active cybercrime organization backed by a nation-state. They’ve been definitively linked to numerous large-scale cryptocurrency thefts, totaling over $7.3 billion. Evidence, including data shown above and recent attacks in April 2026, along with their consistent money laundering methods, strongly supports this conclusion and eliminates most skepticism.
When a cryptocurrency platform loses funds and quickly blames North Korea, ask for solid evidence. See if the claims have been backed up by independent investigations from companies like Chainalysis, Elliptic, or TRM Labs, or confirmed by the FBI or Department of Justice. If that kind of verification isn’t included in the platform’s explanation, the accusation is likely just for publicity.
North Korea often gets blamed as the biggest threat to cryptocurrency, and it’s true they pose a risk. However, the daily problems facing the crypto world are more often caused by poor coding, weak security practices, and even theft from within the industry. It’s important to acknowledge both these external threats and internal weaknesses to move forward honestly.
Read More
- Brent Oil Forecast
- Silver Rate Forecast
- Gold Rate Forecast
- BTC PREDICTION. BTC cryptocurrency
- XRP’s ETF Waltz: $1.2B Inflows, Yet Price Does the Limbo at $1.30
- Stablecoins, RWAs, and the Crypto Industry’s Midlife Crisis
- Mnemonic Mishaps: South Korea’s Tax Agency Seeks Crypto Custodians with a Dash of Decorum
- US and Iran in Pakistan: Crypto’s Wild Ride on a Prayer and a Fragile Peace Deal!
- Bitcoin’s Shocking Plunge: Are We Heading for a Multi-Month Oversold Crisis?
- Canada’s Crypto Crackdown: Democracy or Drama?
2026-04-21 20:23